Email Whitelist-Blacklist Control
Maintainer
Originally developed by Darrell May.
NOTE: This contrib is no longer maintained. There is no guarantee that it will work with the current version of SME server. This contrib needs a new maintainer ****
Description
This contrib provides a server-manager panel to designate user defined email whitelists and blacklists.
An email whitelist is a list of hosts, domains, or email addresses which will be accepted by SME Server regardless of possible spam content or origin. Administrators should use caution when using whitelists as email coming from whitelisted addresses will bypass many of the mechanisms that SME provides for identifying unsafe email messages.
An email blacklist is a list of hosts, domains, or email addresses that will be blocked all of the time.
Installation
Install of the lastest Email Whitelist-Blacklist package is from the smecontribs repo:
1. Install package:
yum --enablerepo smecontribs install smeserver-wbl
2. Reconfigure machine:
signal-event post-upgrade; signal-event reboot
Once you do this a new menu item will be visable in the Server-Manager on the left hand side, called E-mail WBL. Clicking on this will present you with 3 buttons.
E-mail WBL E-mail traffic is scanned and may be blocked due to the various screening methods enabled. You may use this panel to define e-mail white/black lists. Black lists are used for rejecting e-mail traffic. [REJECT] White lists are used for accepting e-mail traffic. [ACCEPT] When completed entering wbls above you must execute the email-update event to restart services and load in your changes. [UPDATE]
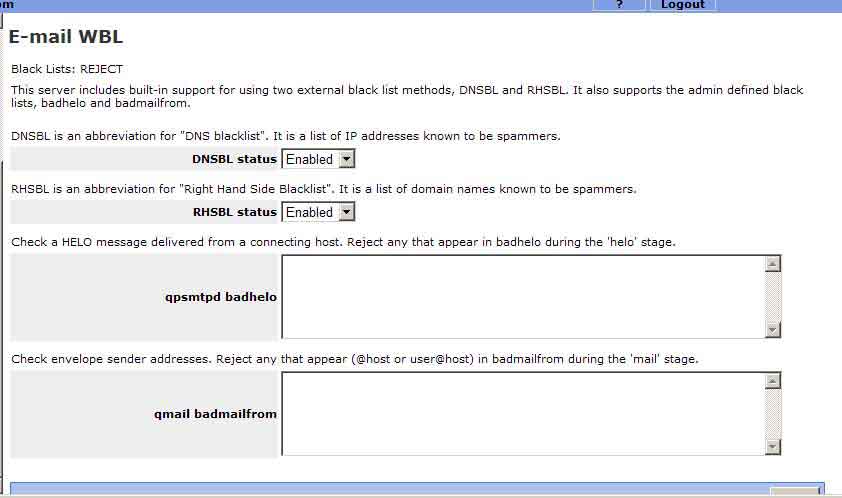
If you press the REJECT button you will see the following window.
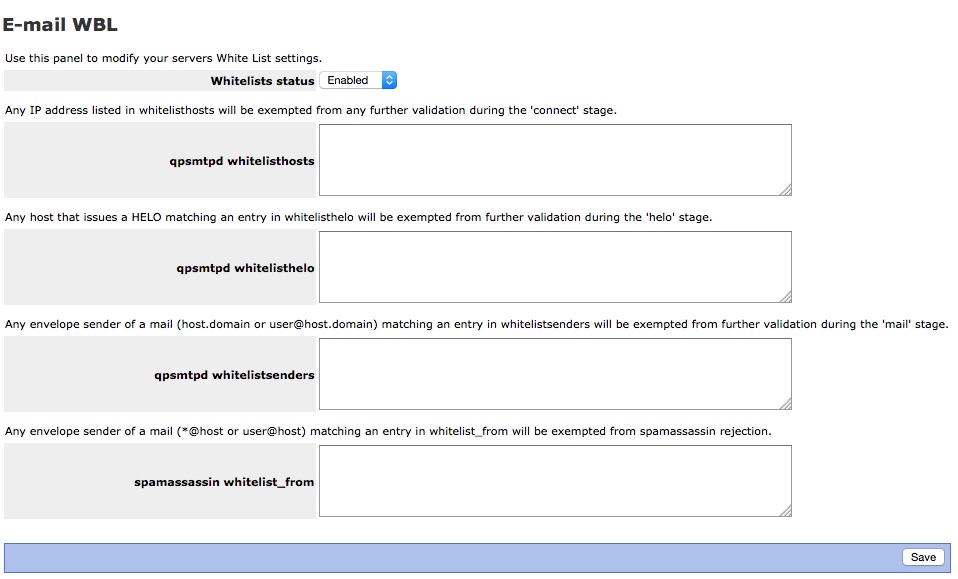
If you press the Accept button you will see the following window.
And finally If you press the UPDATE button you will simply be presented with one button to;
Execute the email-update event now to restart services and load in your changes.
This will apply any of the changes you made in the Reject or Accept windows.
Usage Examples
Black Lists: REJECT
The qpsmtpd badhelo is effective in examining the SMTP HELO string and then block mail based on this string. Entries follow the following format.
something.a.somehost.com
To find the proper string to enter on the qpsmtp badhelo line. 1. Open an offending email. 2. Open the header of the email. 3. Look for a line that says, (HELO something.a.somehost.com) Partial strings will not work, E.G. in the previous example somehost.com will not work. It must be the complete HELO string.
Alternatively you may use the ip address. Again look in the header for the Helo line. It may look something like this,
Received: from smtprelay0207.c.somehost.com (HELO smtprelay.c.somehost.com) (123.111.123.321) Now simply add the IP address you found in the HELO line.
123.111.123.321
Known Issues
Bugs
Please raise bugs under the SME Contribs section in bugzilla .